Posted by: Samker
« on: 16. April 2011., 19:41:07 »Less than a week after warning that hackers were embedding malicious Flash Player files (.swf) into Microsoft Word documents to launch targeted malware attacks, Adobe plans to release an emergency Flash Player patch today to fix the underlying problem.
The patch will fix a “critical” vulnerability in Flash Player 10.2.153.1 and earlier versions for Windows, Mac OS X Linux and Solaris.
According to this Secunia advisory: http://secunia.com/advisories/44119/ , the flaw allows a hacker to completely hijack a vulnerable Windows computer:
A vulnerability has been reported in Adobe Flash Player, which can be exploited by malicious people to compromise a user’s system.
The vulnerability is caused due to an error when parsing ActionScript that adds a custom function to the prototype of a predefined class. This results in incorrect interpretation of an object (i.e. object type confusion) when calling the custom function, which causes an invalid pointer to be dereferenced.
Secunia has posted a technical analysis of the flaw as well: http://secunia.com/blog/210
Adobe has confirmed that the vulnerability (CVE-2011-0611) could cause a crash and potentially allow an attacker to take control of the affected system.
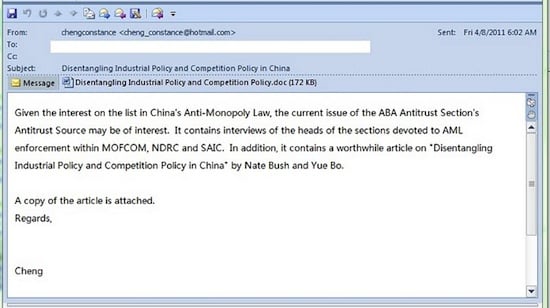
There are reports that this vulnerability is being exploited in the wild in targeted attacks via a malicious Web page or a Flash (.swf) file embedded in a Microsoft Word (.doc) or Microsoft Excel (.xls) file delivered as an email attachment, targeting the Windows platform. At this time, Adobe is not aware of any attacks via PDF targeting Adobe Reader and Acrobat. Adobe Reader X Protected Mode mitigations would prevent an exploit of this kind from executing.
A patch for Google Chrome users is already available in Chrome version 10.0.648.205: http://googlechromereleases.blogspot.com/2011/03/stable-and-beta-channel-updates_15.html
Adobe plans to fix the vulnerability in Adobe Acrobat and Adobe Reader at a later date.
(ZDnet)




 Total Members: 14197
Total Members: 14197