Kaspersky Lab has reported the first sighting of mobile malware (Android, of course) that piggybacks on the back of a separate mobile botnet and uses the resources of other malware once it's installed.
"For the first time malware is being distributed using botnets that were created using completely different mobile malware," said Kaspersky Lab expert Roman Unuchek in a report:
http://www.securelist.com/en/blog/8131/Obad_a_Trojan_now_being_distributed_via_mobile_botnetsThe culprit is trojan called Obad.a, which the company has already branded the most sophisticated piece of mobile malware it has spotted. It comes in 12 flavors so far, and usually spreads via SMS, hacked apps websites, or in the dodgier end of the Android market scene.
Now it appears the Obad boys have teamed up with the makers of malware called Opfake.a, which uses a separate method of propagation by exploiting a flaw in Google Cloud Messaging. GCM was designed to ping out updates and fix phone settings remotely, and allows the sending of 4KB messages to anyone using a specific application.
Kaspersky have found more than a million installers of Opfake in circulation so far. The code sets up a backdoor communications channel to C&C servers, then starts pinging out premium text messages, stealing contacts, and spamming itself outwards – but now some copies are carrying Obad as an extra payload.
Once Opfake is installed, it uses GCM to send out a message of an update (in once case 600 of the things in five hours) and loads Obad.a under the names of mms.apk or mmska.apk. Once installed, the pernicious malware gains Device Administrator privileges and hides itself from file searches, before contacting its C&C servers and spamming itself out in a splurge of activity.
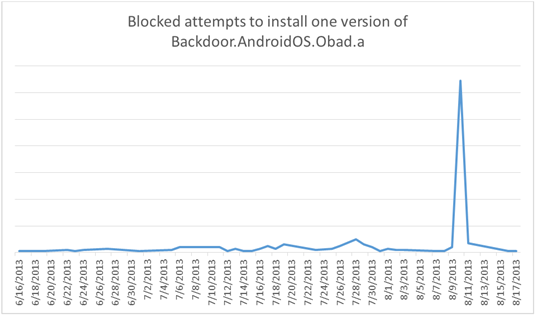
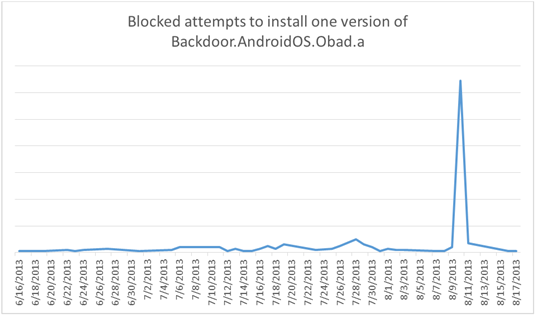
"These peaks are the result of using third-party botnet resources – mobile devices infected with other malware," said Unuchek. "That means that the owners of Backdoor.AndroidOS.Obad.a not only command their own software to spread itself, they also take advantage of Trojans operated by other cybercriminals."
The Obad payload isn't carried on all Opfake samples, and Unuchek concludes that the malware team "rented part of a mobile botnet to spread their brainchild." So far, 83 per cent of Obad infections have come from Russia, with outbreaks reported in Kazakhstan, Uzbekistan, Belarus, and Ukraine.
After consultations with the Chocolate Factory, Kaspersky reports that the flaw that allows Obad to embed itself has been patched, but only in the Android 4.3 build – meaning that unless you have one of a very few Nexus devices, you're wide open.
(ElReg)




 Total Members: 14197
Total Members: 14197