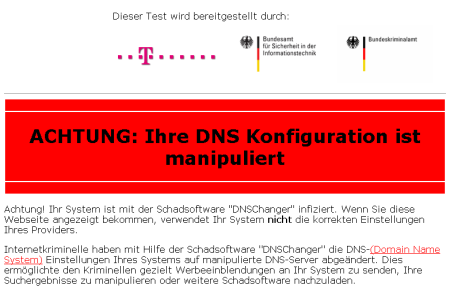
Federal authorities have applied for permission to extend the operation of a safety net that allows machines infected by the DNSChanger Trojan to surf the net as normal beyond a 8 March deadline.
DNSChanger changed an infected system's domain name system (DNS) settings to point towards rogue servers that hijacked web searches and pointed surfers towards various sleazy websites, as part of a long running click-fraud and scareware punting scam.
The FBI stepped in and dismantled the botnet's command-and-control infrastructure back in November, as part of Operation GhostClick:
http://www.fbi.gov/news/stories/2011/november/malware_110911/malware_110911 As many as 4 million machines were infected as the peak of the botnet's activity.
Rogue DNS servers were replaced by legitimate machines at the time of the takedown operation but nothing was done to disinfect infected PCs, a particular concern since the DNSChanger malware is designed to disable security software, leaving infected machines at heightened risk of infection.
Barring court permission, legitimate servers that were set up to replace rogue DNS servers will be taken offline on 8 March, 120 days after the initial takedown operation.
The feds have applied (PDF) to extend this safety net until 9 July: http://krebsonsecurity.com/wp-content/uploads/2012/02/dnschangerextension.pdfA study by security firm Internet Identity revealed that at least 250 of all Fortune 500 companies and 27 out of 55 major government entities had at least one computer or router that was infected with DNSChanger in early 2012, findings that suggest the post-Ghost Click clean-up operation is running behind schedule. Barring an extension in the operation of the surrogate DNS servers these infected machine rely upon, surfers will be unable to browse the web or send emails as normal after 8 March, unless the DNS settings of compromised computer are restored to their original state.
Operation Ghost Click led to the arrest of six Estonian nationals, accused of manipulating millions of infected computers using DNSChanger. The alleged ringleader of the group, Vladimir Tsastsin, and another suspect have been already cleared for extradition to the US. Baltic Business News reports that local courts approved the extradition of the four remaining suspects last week. These extraditions remain subject to government approval but this is all but assured, the local news site reports:
http://balticbusinessnews.com/article/2012/2/21/estonian-court-approves-extradition-of-six-persons-to-us-for-cybercrimeTsastsin previously ran controversial domain registration firm EstDomains, whose accreditation was pulled by ICANN back in 2008 over concerns that EstDomains had become a haven for cybercriminals:
http://voices.washingtonpost.com/securityfix/2008/10/icann_de-accredits_estdomains.htmlKrebsOnSecurity has a copy of the indictment against Tsastsin and other suspects in the GhostClick case here (PDF):
http://krebsonsecurity.com/wp-content/uploads/2011/11/Tsastsin-et-al.-Indictment.pdf(ElReg)
* More information on how to clean up infected machines, and other resources, can be found on the DNS Changer Working Group website here: http://dcwg.org/* Check your computer’s DNS settings - Official FBI instructions and download (PDF): https://forms.fbi.gov/check-to-see-if-your-computer-is-using-rogue-DNS
 Total Members: 14197
Total Members: 14197 Latest: Levine
Latest: Levine Total Posts: 43438
Total Posts: 43438 Total Topics: 16532
Total Topics: 16532 Online today: 3056
Online today: 3056 Online ever: 51419
Online ever: 51419 Total Members: 14197
Total Members: 14197 Latest: Levine
Latest: Levine Total Posts: 43438
Total Posts: 43438 Total Topics: 16532
Total Topics: 16532 Online today: 3056
Online today: 3056 Online ever: 51419
Online ever: 51419